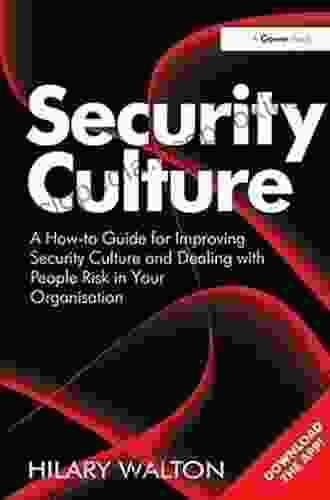
Unlocking Security Culture and People Risk Mitigation: Your Ultimate Guide

In the ever-evolving digital landscape, cybersecurity has become paramount. Organizations are increasingly recognizing the importance of fostering a robust security culture and effectively managing people risk. This article serves as an in-depth guide, providing invaluable insights and practical strategies to elevate your organization's security posture and safeguard against human-related threats.
The Cornerstone: Cultivating a Robust Security Culture
A strong security culture is the bedrock upon which effective cybersecurity practices are built. It encompasses the beliefs, values, and behaviors that permeate every level of an organization, shaping how individuals approach and interact with security matters. Cultivating a robust security culture demands a holistic approach that includes:
5 out of 5
| Language | : | English |
| File size | : | 13674 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 232 pages |
Leadership Commitment:
Senior management must actively demonstrate their commitment to security, allocating resources, establishing clear expectations, and fostering an environment where security is prioritized.
Clear Communication:
Organizations must communicate security policies and procedures effectively, ensuring that all employees understand their roles and responsibilities in safeguarding sensitive information.
Continuous Training and Awareness:
Regular training and awareness campaigns are essential for keeping employees informed about the latest security threats and best practices. By equipping employees with the knowledge and skills they need, organizations can empower them to become vigilant guardians of their organization's data and systems.
Empowered Employees:
A strong security culture empowers employees to report security concerns and participate in security decision-making. Creating channels for employees to voice their observations and suggestions fosters a sense of ownership and enhances the overall security posture.
Addressing People Risk: The Human Factor in Cybersecurity
People risk, stemming from human error, negligence, or malicious intent, poses a significant challenge to cybersecurity. Effectively managing people risk requires organizations to:
Identify and Assess Risks:
Conduct thorough risk assessments to identify potential vulnerabilities and understand the likelihood and impact of various threats. This includes analyzing employee behavior, access levels, and potential for insider threats.
Implement Strong Authentication and Access Controls:
Multi-factor authentication, privileged access management, and role-based access control help restrict access to sensitive data and systems, minimizing the risk of unauthorized individuals gaining access.
Promote Ethical Behavior and Code of Conduct:
Establishing a clear code of conduct that outlines acceptable behaviors and consequences for violations is crucial. This code should be communicated to all employees and reinforced through regular training and awareness campaigns.
Foster an Open and Inclusive Culture:
Creating a work environment where employees feel comfortable reporting security concerns or mistakes without fear of retaliation encourages transparency and early identification of potential threats.
Practical Strategies for Enhancing Security Culture and Mitigating People Risk
Implementing the following strategies can significantly enhance your organization's security culture and mitigate people risk:
Establish a Security Champions Program:
Identify and appoint security champions throughout the organization who serve as ambassadors for security awareness and best practices. These individuals can help foster a positive security culture and promote security consciousness among their peers.
Conduct Regular Security Assessments:
Regularly assess the effectiveness of your security culture and identify areas for improvement. This includes conducting security audits, evaluating employee behavior, and reviewing security incident reports.
Encourage Employee Participation in Security Initiatives:
Involve employees in security decision-making and encourage their participation in security awareness programs. By giving them a voice, organizations can tap into their valuable insights and foster a sense of ownership over security.
Utilize Technology to Support Security Culture:
Leverage technology to automate security tasks, simplify policy enforcement, and enhance threat detection and response. Security information and event management (SIEM) solutions, intrusion detection systems (IDS),and security awareness training platforms can augment human efforts and strengthen security posture.
Foster a Continuous Learning Environment:
Security threats are constantly evolving, making continuous learning essential for maintaining a robust security culture. Provide ongoing training and resources to keep employees updated on the latest threats and best practices.
Case Study: Implementing a Successful Security Culture
Company XYZ, a leading healthcare provider, successfully implemented a comprehensive security culture program. By establishing a clear security policy, conducting regular training, and empowering employees to report security concerns, they significantly reduced the number of security incidents. Furthermore, by creating a culture of trust and open communication, employees felt comfortable reporting potential threats, enabling the organization to proactively address risks and prevent security breaches.
Cultivating a strong security culture and effectively managing people risk are critical for organizations seeking to safeguard their data and systems against cyber threats. By implementing the strategies outlined in this guide, organizations can create an environment where security is valued, employees are empowered, and risks are proactively mitigated. By investing in a robust security culture, organizations can strengthen their defenses, enhance resilience, and maintain a competitive edge in the face of evolving cybersecurity challenges.
5 out of 5
| Language | : | English |
| File size | : | 13674 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 232 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Alan Bell
Alan Bell Adolf Hungry Wolf
Adolf Hungry Wolf Aesop
Aesop Adam Makos
Adam Makos Aaron Marcus
Aaron Marcus Alex North
Alex North Abridged Ed Edition Kindle Edition
Abridged Ed Edition Kindle Edition Abraham Lincoln
Abraham Lincoln Abul K Abbas
Abul K Abbas Akash Kapur
Akash Kapur Alex Bell
Alex Bell Adam Mckeown
Adam Mckeown Aaron Muller
Aaron Muller Adedayo Phillips
Adedayo Phillips 2013th Edition Kindle Edition
2013th Edition Kindle Edition Aaron Reynolds
Aaron Reynolds Alan Rusbridger
Alan Rusbridger Adrian Leonard
Adrian Leonard Aabis Johnson
Aabis Johnson Aaron Oster
Aaron Oster
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Russell MitchellThe Enchanting World of "The Fir Tree Hetherington": A Literary Journey into...
Russell MitchellThe Enchanting World of "The Fir Tree Hetherington": A Literary Journey into...
 Kazuo IshiguroPolicy and Planning Inside Global City ISSN: Your Essential Guide to Urban...
Kazuo IshiguroPolicy and Planning Inside Global City ISSN: Your Essential Guide to Urban...
 Samuel Taylor ColeridgeThe Rise and Impact of Italian Cooperatives: A Historical and Economic...
Samuel Taylor ColeridgeThe Rise and Impact of Italian Cooperatives: A Historical and Economic...
 Shawn ReedUnlock the Secrets of Chinese Postpartum Recovery with "An American Mother's...
Shawn ReedUnlock the Secrets of Chinese Postpartum Recovery with "An American Mother's... Levi PowellFollow ·14.5k
Levi PowellFollow ·14.5k Isaias BlairFollow ·3.1k
Isaias BlairFollow ·3.1k Andy ColeFollow ·17.3k
Andy ColeFollow ·17.3k Fletcher MitchellFollow ·2.6k
Fletcher MitchellFollow ·2.6k Larry ReedFollow ·13.2k
Larry ReedFollow ·13.2k Eugene ScottFollow ·10.2k
Eugene ScottFollow ·10.2k Colt SimmonsFollow ·2.1k
Colt SimmonsFollow ·2.1k Virginia WoolfFollow ·17.8k
Virginia WoolfFollow ·17.8k
 Francis Turner
Francis TurnerArt and Politics in the Shadow of Music
Music has...
 Jaylen Mitchell
Jaylen MitchellHow Algorithms Are Rewriting The Rules Of Work
The workplace is...
 Chandler Ward
Chandler WardRio de Janeiro & Minas Gerais Footprint Handbooks:...
Embark on an extraordinary adventure through...
 David Mitchell
David MitchellThe Story of Depression: Understanding and Treating a...
Delving into the Shadows of...
 Al Foster
Al FosterStatistics Done Wrong: The Woefully Complete Guide
Tired of being...

 DeShawn Powell
DeShawn PowellJulia Child's Second Act: A Tale of Triumph,...
Julia Child is an...
5 out of 5
| Language | : | English |
| File size | : | 13674 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 232 pages |